What is network segmentation for energy systems?
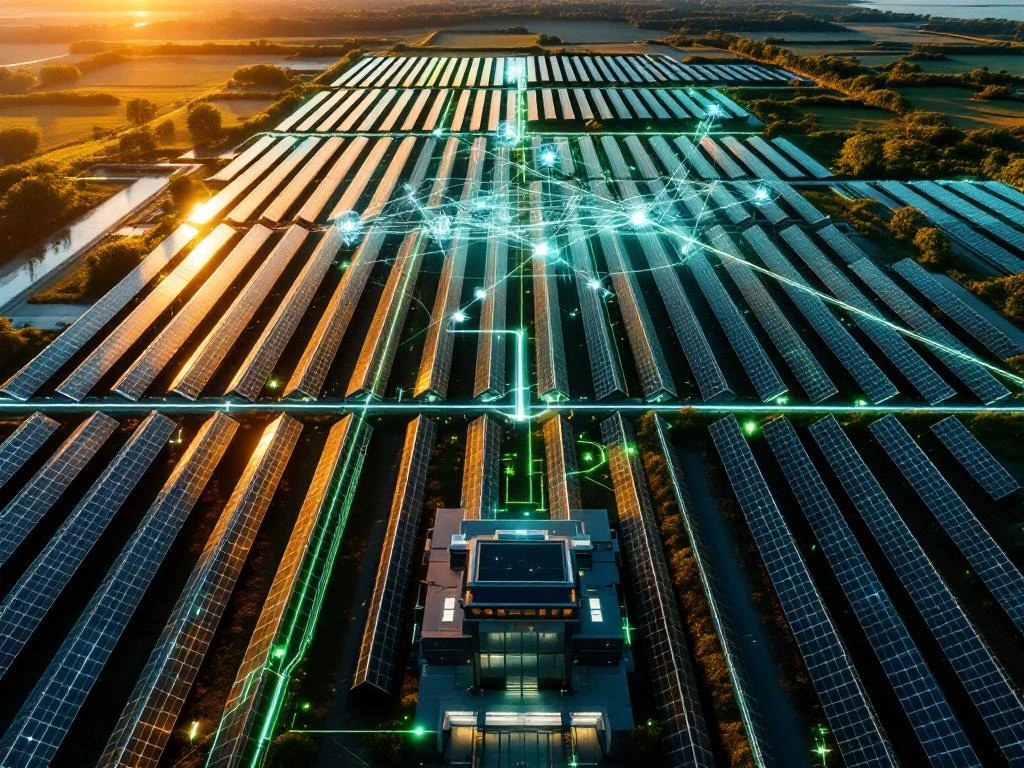
Network segmentation for energy systems divides renewable energy infrastructure into separate, secure network zones to protect against cyber threats. This cybersecurity approach creates security boundaries within solar farms, energy storage installations, and smart grid connections, preventing attackers from moving laterally through connected systems. Energy systems face unique vulnerabilities due to their critical infrastructure status and increasing connectivity requirements.
What is network segmentation and why do energy systems need it?
Network segmentation creates isolated security zones within energy infrastructure by separating different system components into distinct network areas. This approach prevents cyber attackers from accessing multiple systems if they breach one component, containing potential damage within specific network segments.
Energy systems require network segmentation because they present attractive targets for cybercriminals and nation-state actors. Solar energy projects, battery storage systems, and smart grid connections increasingly rely on internet-connected devices for monitoring, control, and data collection. These interconnected systems create multiple entry points that attackers can exploit to disrupt power generation, steal sensitive data, or manipulate energy distribution.
The critical nature of energy infrastructure makes power grid protection particularly important. A successful cyberattack on renewable energy networks can affect thousands of homes and businesses, making proper security measures essential for maintaining a reliable energy supply. Network segmentation reduces these risks by limiting how far attackers can penetrate energy system infrastructure.
How does network segmentation work in solar energy projects?
Solar energy cybersecurity implementation involves creating separate network zones for different system components, including inverters, monitoring equipment, and grid connection points. Each zone operates independently while maintaining controlled communication channels between necessary components.
In practical terms, solar farm network security typically includes three main zones. The operational technology zone contains inverters, power optimizers, and physical control systems that directly manage energy production. The information technology zone houses data collection systems, monitoring software, and administrative interfaces. The demilitarized zone acts as a buffer between internal systems and external internet connections.
Communication between these zones occurs through secure gateways that monitor and filter all data exchanges. For example, monitoring data from inverters passes through security controls before reaching the administrative systems, while external internet access requires additional authentication and encryption protocols.
What are the main security risks that network segmentation prevents?
Network segmentation prevents malware propagation, unauthorized system access, and manipulation of energy production controls. Without proper segmentation, attackers who compromise one system component can move laterally through connected networks to access critical infrastructure controls.
Common cyber threats targeting renewable energy networks include ransomware attacks that encrypt operational data, advanced persistent threats that steal intellectual property, and denial-of-service attacks that disrupt energy production. Attackers may also attempt to manipulate inverter settings, alter monitoring data, or gain access to grid connection controls.
Smart grid segmentation specifically addresses risks related to bidirectional energy flow and real-time communication requirements. These systems face additional threats from data interception, false command injection, and timing attacks that could destabilize grid operations. Proper segmentation ensures that compromised monitoring systems cannot affect critical control functions.
Which components of energy systems should be segmented?
Critical infrastructure elements requiring network isolation include control systems, monitoring devices, communication networks, and administrative interfaces. Priority should be given to components that directly control energy production or connect to external networks.
Control systems such as inverter management platforms, battery management systems, and grid connection equipment require the highest level of protection through dedicated network segments. These systems directly affect energy production and safety, making unauthorized access particularly dangerous.
Data collection and monitoring components, including weather stations, performance meters, and remote monitoring software, should operate in separate network zones from control systems. Communication infrastructure such as wireless access points, network switches, and internet gateways needs individual security boundaries to prevent it from becoming an attack vector.
Administrative systems, including user management interfaces, maintenance scheduling software, and financial reporting platforms, require segmentation from operational components. This separation ensures that energy infrastructure security breaches in administrative systems cannot compromise energy production capabilities.
How do you implement network segmentation for renewable energy projects?
Implementation begins with comprehensive network mapping to identify all connected devices, communication pathways, and data flows within the renewable energy system. This assessment reveals which components require isolation and how they need to communicate securely.
The technical implementation involves configuring firewalls, network switches, and access controls to create distinct security zones. Each zone receives specific security policies that govern which devices can communicate with other network segments. Virtual local area networks and software-defined networking technologies help create these logical separations within physical network infrastructure.
For existing renewable energy installations, retrofitting network segmentation requires careful planning to avoid disrupting ongoing operations. This process typically involves:
- Conducting security assessments during maintenance windows
- Gradually implementing segmentation controls in phases
- Testing communication pathways before full deployment
- Training operational staff on new security procedures
Ongoing maintenance includes regular security monitoring, access control updates, and periodic assessments to ensure segmentation remains effective as systems evolve. Thorough inspections and assessments require continuous attention to address new threats and technology changes.
How Solarif helps with network segmentation for energy systems
We support renewable energy projects with comprehensive cybersecurity assessments and network security planning services. Our expertise in energy infrastructure security helps you identify vulnerabilities and implement appropriate segmentation strategies for your specific installation requirements.
Our network segmentation services include:
- Cybersecurity assessments for solar and renewable energy projects
- Network security architecture design and implementation planning
- Compliance guidance for industry security standards and regulations
- Insurance coverage evaluation for cyber risks in energy systems
- Ongoing security monitoring and inspection support
As an insurance broker specializing in renewable energy projects, we understand how proper network segmentation affects insurance coverage and security profiles. We help you meet insurer requirements for cybersecurity controls while ensuring your energy systems remain secure and operational.
Contact our cybersecurity experts today to discuss network segmentation strategies for your renewable energy project and ensure comprehensive protection against cyber threats.
Insurance and inspection needs for your BESS?
Contact us today if you want to know more about the possibilities in BESS insurance and Scope inspections.
📧 Email: support@solarif.com
☎️ Phone: +31 (0)26 711 5050




